
Is your office on a WiFi hotspot? Do you connect to your local Starbucks, hotel, or at the gym? Chances are you connect to WiFi to save from costly cellular data plans.
Also, as more and more enterprises are enabling WiFi these access points are ripe for malfeasance. Let’s look at a WiFi kill-chain to understand where the vulnerabilities are and what controls should be put in to place.
WiFi Broadcast (Reconnaissance) – The first step is WiFi discovery through SSID (Service Set Identifier). This is the WiFi you would connect to in let’s say a Starbucks. If you’re Starbucks then you’d want to broadcast your SSID but if you’re a bank that’s probably not a good idea.
Rather you broadcast or not it is pretty easy to be found. First its important to remember that WiFi is radio waves. So, like a radio if you have a tuner you can pick up the frequency waves and sniff traffic. WiFi gateways will talk over different frequencies and channels. For us old timers you can remember when the first cordless home phones came to market as they all had a channel button as interference was common in those days.
Most WiFi cards have the ability to act in promiscuous mode. This mode allows for the card to capture packets “over the air”. OFDM (Orthogonal Frequency-Division Multiplexing) helps as it allows for jumping across the WiFi spectrum (think 802.11x splashed on cover of router boxes at BestBuy) but ultimately this is why we have encryption.
Reconnaissance tools are easily available for download. The output of just listening to radio waves is astonishing. 
WiFi Encryption (Attack)
WEP (Wired Equivalent Privacy) – 1 out of 4 enterprise are running WEP which is a major vulnerability. WEP encryption standard was based on RC4 which only made cryptographic algorithms weaker. If you are connecting to this you better beware! WEP is very weak for 3 reasons:
- Shared Key Algorithm in which in some cases you only need the correct SSID value to authenticate to the Access Point.
- Even with SKA enabled there is poor use of initialization vectors
- Static encryption keys
- For extra credit ICV (integrity check values) can easily be manipulated meaning data can easily be modified by flipping specific bits.
If you are using WEP you’re a soft target. In fact to crack WEP is only going to take about 3 seconds on a Pentium M processor. This could easily be done by just walking the hall in an office building.
The good news in our scan above WEP is not enabled, but the bad news is that some don’t have any encryption at all. As an end-user shopping online at the local coffee shop beware. You don’t want to connect to an AP (access point) that does not use WPA2.
No encryption means no cracking. Just capturing the data is enough to cause significant damage! Airsnort and WEPCrack are two common tools known to crack WEP.
WPA (Wi-Fi Protected Access) – Introduces TKIP (Temporal Key Integrity Protocol) which improves the security of WEP. The reason for the prevalence of WPA is that it does not require a hardware upgrade. TKIP provides a key mixing function which allows for RC4 to provide a higher degree of protection.
WPA encryption is broken down as (WEP Key + IV value + MAC Address = New Encryption Key). This means to crack WPA your going to need some horsepower. WPA 2 uses the latest AES in CTR mode which makes it almost impossible to crack.
With WPA or WPA2 most often the fastest way to crack the AP is through the password after discovery.
Three ways to crack a password:
Dictionary Attack – This attack uses a list of common used passcodes and retries until the crack occurs.
Cryptography – Initialization Vectors in WEP made this easy. Much more difficult with WPA2.
Bruteforce – This doesn’t use a list rather tries every possible combination – slow are arduous.
Cracking the AP is going to require capturing the 4 way handshake. In 4 way handshake the AP sends ANonse to client, which is basically a random integer. Client use the ANonce and PMK to generate the PTK (Pairwise Transient Key), then sends a CNonce (Client Nonce) and MAC. AP sends MAC and GTK (Group Temporal Key) to client.
Once this is capture you can begin to crack the password. You’ll need to have a supported chipset that has the ability to perform injections. Injection allows for spoofing and to appear part of the network traffic flow. This is important as the 4-way handshake has to be capture and used as part of the cracking.
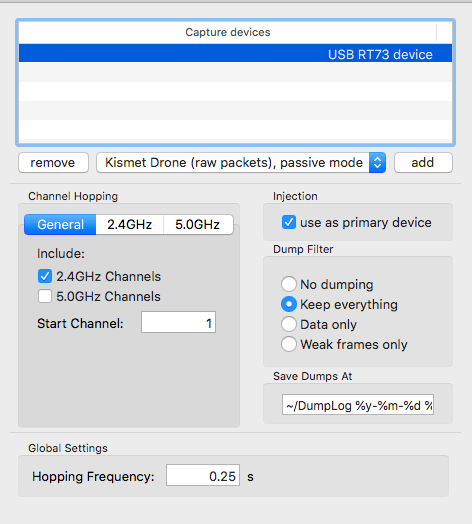
It easy to purchase the appropriate chipset and will only cost about $20. In this research a RT73 Chipset was used.

Capturing the 4-way handshake can take some time. One option is to try to force the AP to reboot to capture the 4-way. This can be accomplished by trying a deauthentication/authentication attack that will reboot the wireless gateway. Once all the data is capture you’ll want to use this for injection and the appropriate dictionary.

One tool commonly used is aircrack-ng. Using the output from capture you can execute a password crack on WPA / WPA2.
Most enterprise will deploy WPA2 Enterprise thus allowing for EAP (Extensible Authentication Protocol). By using EAP enterprises can decide how to further encapsulate packs with EAP-TTLS, EAP-PEAP (the 2 most common) or other options.
In order to crack WAP2 Enterprise will require a man in the middle attack. This type of attack will require users to connect to faux AP. The AP needs to replicate the target network and spoofing the target network to the fake access point (by providing a stronger signal users will more likely connect to the fake AP).
In order to create a fake AP proximity is important as well as replication of network. A quick way is to stand up a free RADIUS server using some basic CLI commands. FreeRADIUS was used in this research.
$ wget ftp://ftp.freeradius.org/pub/radius/old/freeradius-server-3.0.17.tar.bz2
At this point its important to note that a validate certificate must be setup for the AP in order for the client to connect. The final step is to turn our network adapter into a fake AP. We can do this by using Hostapd which is a software approach to turning a NIC card into an Access Point.
wget http://hostap.epitest.fi/releases/hostapd-2.3.tar.gz
Once Hostapd is installed you’ll want to configure to mimic the target network. Some examples would be to set the interface and SSID:
interface=wlan0 # Interface used for Access Point
ssid=EnterpriseWireless # SSID of wireless network
Once the configuration is completed you can then start the AP and start accepting connections. Once clients connect you can simply capture the traffic; send it to fake destinations, etc.
Conclusion – Introducing WiFi has many advantages but comes with risk. By using the latest in wireless technology the risk can be limited.
Its important to have a thorough Security Awareness Program that can help teach employees about the dangers of connecting to untrusted AP points which is one of the biggest threats next to misconfigured gateways.
Every organization should be scanning for fake AP and taking them down. Also as part of your penetration scope you should include WiFi access points.
Finally, for the home you should be aware of unauthorized users. There’s been cases where unauthorized users piggybacked on a home WiFi and used the access point to illegally download music, videos, etc. It’s important to use long and strong passwords. Remember this also means the admin account for your home router!